The Invisible Hijack: Understanding SIM Swapping in 2026
- echoudhury77

- 14 minutes ago
- 3 min read
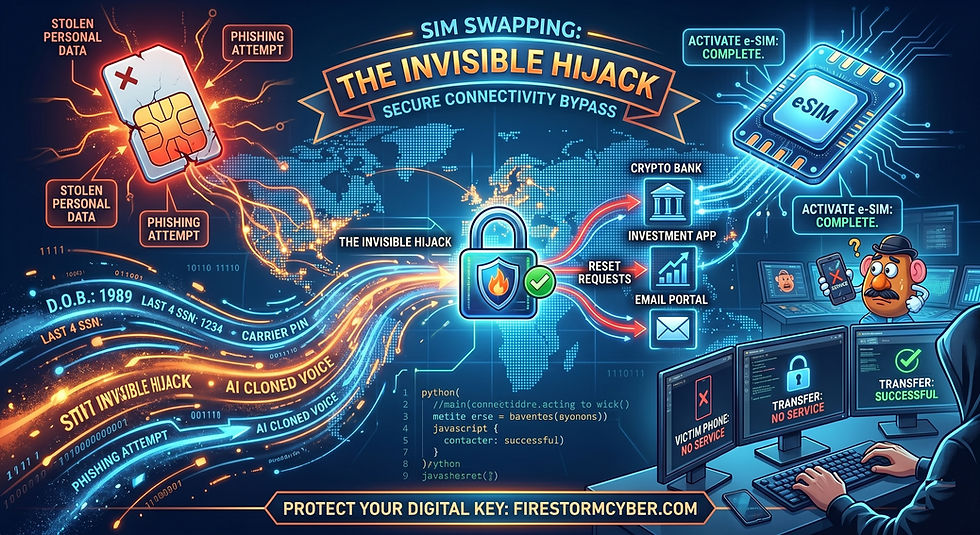
Imagine waking up, reaching for your phone, and seeing "No Service." You toggle Airplane Mode, you restart the device—nothing. While you’re troubleshooting your signal, a hacker miles away is currently using your phone number to drain your bank account, reset your email passwords, and bypass your Multi-Factor Authentication (MFA).
This is SIM Swapping (also known as "simjacking" or a "port-out scam"), and in 2026, it has become one of the most surgical and devastating forms of identity theft.
What Exactly is a SIM Swap?
Most of us use our phone numbers as a "digital skeleton key." We use them for password recoveries and to receive those 6-digit SMS codes for 2FA.
A SIM swap happens when a criminal convinces your mobile carrier to transfer your phone number to a SIM card (or eSIM) that they control. Once the transfer is complete, your physical phone becomes a paperweight, and the hacker’s device becomes the "trusted" receiver for all your private calls and messages.
How the Heist Happens: The 3-Step Process
1. The Information Harvest
A hacker doesn't start with your phone; they start with your data. Using phishing emails, social media "doxing," or purchasing info from dark web data breaches, they gather:
Your full name and address.
Your Date of Birth.
The last four digits of your Social Security Number.
The name of your mobile carrier.
2. The Social Engineering Play
Armed with your profile, the hacker calls your carrier’s customer support. They pose as you, claiming they’ve "lost their phone" or "bought a new device and need to activate an eSIM." If the customer service representative is tricked by the hacker's "stolen" personal details, they authorize the swap.
Note: In some high-stakes cases, hackers have even bribed or "phished" carrier employees directly to bypass security protocols.
3. The Digital Takeover
The moment your service bars vanish, the hacker’s phone goes live. They immediately visit your banking or crypto exchange apps and click "Forgot Password." The recovery code is sent via SMS to their device. They reset your password, log in, and move your funds before you've even finished your first cup of coffee.
The 2026 Reality: eSIMs and AI
As we move further into 2026, two factors have accelerated these attacks:
eSIM Speed: With traditional SIM cards, a hacker had to wait for a physical card or go to a store. With eSIM technology, a number can be "ported" and activated digitally in under five minutes.
AI Voice Cloning: Sophisticated attackers are now using AI to clone a victim's voice from a short social media clip, making their impersonation of you to the phone company nearly indistinguishable from the real thing.
How to Protect Your "Digital Key"
Security Level | Action to Take |
Carrier Level | Call your provider and add a "Port-Out PIN" or "SIM Protection Lock." This requires a secondary password before any SIM changes can be made. |
Authentication | Stop using SMS-based 2FA. Switch to Authenticator Apps (like Google or Microsoft) or hardware keys (like YubiKey) that don't rely on a phone signal. |
Privacy | Be stingy with your phone number. Don't post it on social media or use it for "loyalty programs" that aren't strictly necessary. |
Response | If your phone suddenly loses service for no reason, contact your carrier immediately from a different line. |
SIM swapping turns your greatest convenience—your smartphone—into your greatest vulnerability. By moving away from SMS-based security and locking down your carrier account, you can ensure your "No Service" bars are just a glitch, not a robbery.
Is your business still relying on SMS codes for employee logins? It might be time for a security audit.
Firestorm Cyber: Securing the Future, Component by Component.




Comments